What You Need
GDB is the gold standard for debugging on.nix. GDB has all of the debugging features you would expect in a modern debugger. For example, reverse debugging is the best feature to have if you are modifying the binary in memory, when you make a mistake just step back and try again. Jul 05, 2018 You are downloading OllyDbg, version 2.01. Each download we provide is subject to periodical scanning, but we strongly recommend you check the package for viruses on your side before running the installation. This download is absolutely FREE. The contents of the download are original and were not modified in any way.
A Windows machine, real or virtual. I used a Windows Server 2008 virtual machine.Purpose
To modify a Windows EXE file and save an altered version.This gives you practice with very simple features of theOllydbg debugger.Get putty.exe
If you are using the machine handed outby your instructor, putty.exe is inthe Downloads folder.If you are using some other machine,get it here:
Verifying the SHA256 Hash
Run Hashcalc on putty.exe andconfirm that the SHA256 value matchesthe value shown below.Running Putty
Double-click putty.exe. PuTTY opens, as shown below.If PuTTY won't start, right-click it, click Properties,and click Unblock.
In the 'Host Name (or IP address)' box, type
ad.samsclass.infoA black box opens, and shows a 'login as:'prompt, as shown below.
You could connect to a server at this point,but that's not the point of this project.We will alter this program to do other thingsinstead of printing 'login as'.
Close the Putty window.
Starting Ollydbg
Click Start. Search for Ollydbgand start it.In Ollydbg, from the menu bar, clickFile, Open. Navigate toputty.exe and open it.
Ollydbg opens, as shown below. If yourscreen doesn't look like this, clickView, CPU and maximize theCPU window.
Ollydbg shows you a lot of data,but for now just notice theAssembly Code in the topleft pane, and the Pausedmessage in the lower right.
When you load a program into Ollydbg,it starts in a 'Paused' state,with the Assembly Code window showingthe first instruction.
Running Putty in Ollydbg
In Ollydbg, from the menu bar,click Debug, Run.A Putty window opens,but it's behind the Olly window.At the bottom of the screen,in the taskbar, click the'PuTTY Configuration'button to bring the PuTTY windowto the front,as shown below.
Click in the Putty window.In the 'Host Name (or IP address)' box, type
ad.samsclass.infoPutty is running, but it's under the controlof Ollydbg, so we can modify its execution.
Finding the 'login as' Code
Close the Putty window. A boxasks 'Are you sure...' ClickOK.In Ollydbg, from the menu bar,click Debug, Restart.
In Ollydbg, in the 'Assembly Code'pane, right-click. Point to'Search for'. Click'All referenced text strings',as shown below.
A'Text strings referenced in putty:.text'window opens, showing all thestrings in the program.
To make this text easier to read,right-click, point toAppearance,Font, and click'OEM Fixed Font'.
Right-clickin that window, and click'Search for text',as shown below.
In the 'Enter text to search for' box,type
login asClick OK.
Ollydbg finds the ASCII string 'login as',and the instruction that uses it,as shown below. This instructionis at address 00417053.
Right-click again, and click'Search next'.
Ollydbg finds another line of codethat uses this string,as shown below. This instructionis at address 0041CB6E.
Right-click again, and click'Search next'.
A message appears at the bottom of thewindow saying 'Item not found'.There are only two commands in theprogram that use this string.
Using Breakpoints
We'll set breakpoints at those instructionsto see which one is used when logging into an SSH server.In the 'Text strings referenced in putty:.text'window,right-click again, and click'Search text'. In the'Enter text to search for' box,click OK.
The instruction at 00417053 appears again.Right-click this instruction andclick 'Toggle breakpoint',as shown below.
Ollydbg For Macvirtuallasopa 2
The address turns red,as shown below, to indicate thatthere's a breakpoint here.
Right-click again, and click'Search next'. The instructionat address 0041CB6E appears.Right-click it andclick 'Toggle breakpoint'.
The address turns red,as shown below.
In Ollydbg, from the menu bar,click Debug, Restart.
A box pops up warning you that'Process 'putty' is active'.Click Yes.
In Ollydbg, from the menu bar,click Debug, Run.
A Putty window opens. Bring it to thefront, as shown below.
Click in the Putty window.In the 'Host Name (or IP address)' box, type
ad.samsclass.infoA black window opens and closesquickly, and the programstops,as shown below.
The program stopped at instruction0041CB6E, as shown in the image above.
We'll use this instruction to hijack theprogram's execution.
Removing the Breakpoints
We don't need the breakpoints any more,so we'll remove them.In Ollydbg, from the menu bar,click View, Breakpoints.
A 'Breakpoints' window opens, showingtwo breakpoints.
Right-click the first breakpoint and clickRemove, as shown below.
Repeat the process to removethe other breakpoint. Close the'Breakpoints' window.
Removing One Letter From the Message
In Ollydbg, in the CPU window, in theAssembly Code pane, right-click theinstruction at address 0041CB6Eand click Assemble,as shown below.An 'Assemble at 0041CB6E' box appears,as shown below.
This shows the command at this location. It'sa PUSH instruction, placing the address467C7C onto the stack. That addresspoints to the letter 'l' in the ASCII string'login as: ', as shown on the right sideof the instruction line, outlined in greenin the image below.
In the 'Assemble at 0041CB6E' box, changethe last character to D,as shown below. This will move thepointer from the 'l' to the 'o' in thestring 'login as: '.
Click the Assemble button.
Click the Cancel button.
The message on the right now says'ogin as: ',as shown below.
Running the Modified Program
In Ollydbg, from the menu bar,click Debug, Run.The black login window appears,with the message 'ogin as: ',as shown below.
When I did it, an error box alsopopped up saying 'Server unexpectedlyclosed network connection'. If that happens,just close the error box.
Saving the Modified .text Section
We have now changed an assembly languageinstruction; all executable code isin the .text section of the file.In Ollydbg, in the top left pane of theCPU window, right-click, point to'Copy to Executable',and click 'All modifications',as shown below.
A 'Copy selection to executable file' boxpops up, as shown below.Click the 'Copy all'button.
A new window pops up, with a title ending in'putty.exe', as shown below.
Right-click in the new window and click'Save file'.
Save the file as puttymod.exe.
Running the Modified EXE
Close Ollydbg.Double-click puttymod.exe.
In the 'Host Name (or IP address)' box, type
ad.samsclass.infoA black box opens, and shows a 'ogin as:'prompt, as shown below.
Modifying the puttymod File
Open Ollydbg and load the puttymod.exefile.In the top left pane of the CPU window,right-click, point to'Go to', and clickExpression,as shown below.
In the 'Enter expression to follow' box,enter
41CB6Eas shown below. Click OK.
Changing the Login Message
In the top left pane of the CPU window,right-click 00467C7D,as shown below. Point to'Follow in Dump' andclick 'Immediate constant'.The Hex Dump pane, inthe lower left, shows the text'ogin as: ',as shown below.
In the Hex Dump pane,highlight 'ogin as:',as shown below. Right-click thehighlighted text.Point to Binary.Click Edit.
An 'Edit data at 00467C7D' boxopens,as shown below.
Click in the ASCII field, press Backspaceto move back to the start, andoverwrite the message with this text,as shown below:
BADNESS
Click OK.The modified text appears in redletters in the Dump,as shown below.
Saving the Modified ASCII Text
In Ollydbg, in the lower left 'Dump' pane of theCPU window, right-click and click'Copy to executable file',as shown below.A boxwith a long title ending in'puttymod.exe'appears showing the modifiedfile, as shown below. Click theX in the top right of thatbox to close it.
A 'File changed' box appears, asshown below. Click Yes.
A 'Copy selection to executable file' boxpops up. Click the 'Copy all'button.

A new window pops up, with a title ending in'putty.exe', as shown below.
Right-click in the new window and click'Save file'.
Save the file as 'puttymod2.exe'.
Running the Modified EXE
Close Ollydbg.Double-click puttymod2.exe.
In the 'Host Name (or IP address)' box, type
ad.samsclass.infoOllydbg For Macvirtuallasopa Free
Open button.A black box opens, and shows a'BADNESS:'prompt, as shown below.
Calculating the Hash (20 pts)
Calculate the CRC32 hash puttymod2.exeUse the formbelow toget your points.
Sources
Backdooring PE Files - Part 1Art of Anti Detection 2 – PE Backdoor Manufacturing
https://github.com/EgeBalci/Cminer
https://en.wikipedia.org/wiki/Code_cave
http://stackoverflow.com/questions/787100/what-is-a-code-cave-and-is-there-any-legitimate-use-for-one
The Beginners Guide to Codecaves
Reversing with Ollydbg debugger
Ollydbg 'Copy all modifications to executable' doesn't copy all modificationsRevised 1-7-19
What You Need
- A Windows machine, real or virtual. I tried this on Windows 7, 10, and Server 2008 and itworks on them all.
Summary
This is just the beginning of Lab09-01,performing the first run-through.This analysis shows that if the code isexecuted as it is, it checksfor a certain registry key, and ifthat key is absent, it deletes itself.
Get OllyDbg 1.10
Get OllyDbg 1.10 here:Don't waste your time on OllyDbg 2.00 or 2.01.They are both broken.
Finding the Main Entry Point
Open the Lab09-01.exe file in IDA Pro.Click Options, General.Check 'Line Prefixes', asshown below.
Click OK.
Click Windows, 'ResetDesktop'.
IDA Pro shows that main startsat 0x402AF0, as shown below:
Saving the Screen Image
Make sure you can see the0x402AF0 address,as shown above.On your keyboard, press the PrntScrn key.

Click Start, type in PAINT, andopen Paint.
Press Ctrl+V to paste in the image of yourdesktop.
YOU MUST SUBMIT WHOLE-DESKTOP IMAGES TO GET FULL CREDIT.
Save the imagewith a filename of 'Proj 11a from YOUR NAME'.
Using OllyDbg to Walk Through Quickly
Open Lab09-01.exe in OllyDbg.You start at a preamble, which comesbefore the entry pointyou saw in IDA Pro, as shown below.
Press F8 forty times, to step over untiladdress0x403933. In the upper left paneof OllyDbg, scroll down a few lines to showthe code that setsthe arguments and calls main,as highlighted below.
Press F7 five times to load parameters and call mainfrom 0x403945, showing a new section of codestarting at 0x402AF0,as shown below.
Press F7 twenty-one times to call a short subroutineand get to 0x402AFD,as shown below.
This CMP operation is testing tosee if the number of command-linearguments is 1.
Press F7 three times to pass thetest and jump to0x00401000, as shown below.
Now we are in the routine starting at0x401000.
It calls RegOpenKeyExA at 0x40101B.
Left-click the line starting with0x401021 and press F2 to put abreakpoint there. That address turnsred, as shown below.
Left-click the line starting with0x401000. Press F9 to run to thebreakpoint.
Look at the upper right to see theregisters. EAX now contains 2,as shown below.
This is a 'non-zero error code',as explained here:
That means the test failed--it did not findthe registry key it was looking for.
Press F7 three times to get to location 0x401027.
Press F7 to execute the JMP.
Press F7 three times to step through the subroutine andget to 0x402B08.
Press F7 three times to get to location0x402410, as shown below:
This function uses GetModuleFilenameto get the path to the current executableand builds the ASCII string
/c del path-to-executable >> NULTo see that, place a breakpoint just afterGetShortPathNameA, so its addressturns red, as shown below.
Click the line starting with0x402410 to highlight it.
Press F9 to run to the breakpoint.
You should now be at the line ending with'ASCII '/c del ',as shown below.
By holding F7 down or tapping it many times,you can play thecode forward like a movie in slow motion.
Watch as the code slowly steps through a longpath name in EDI. Then the path name flips quickly throughseveral registers, ending up in EDX.
Stop when you see a stringin EDX, starting with
ASCII '/c del C:
as shown below:
TroubleshootingIf you press F7 too many times, EDXempties. To return to this point youmust do these steps:
|
Saving the Screen Image
Ollydbg For Macvirtuallasopa Windows
Make sure you can see theEDX register with a valuestarting withASCII '/c del C:as shown above.On your keyboard, press the PrntScrn key.
Click Start, type in PAINT, andopen Paint.
Press Ctrl+V to paste in the image of yourdesktop.

YOU MUST SUBMIT WHOLE-DESKTOP IMAGES TO GET FULL CREDIT.
Save the imagewith a filename of 'Proj 11b from YOUR NAME'.
Turning in Your Project
Email the images to: cnit.126sam@gmail.comOllydbg For Macvirtuallasopa Mac
with a subject line of Proj 11 From Your Name,replacing Your Name with your own first and last name.Send a Cc to yourself.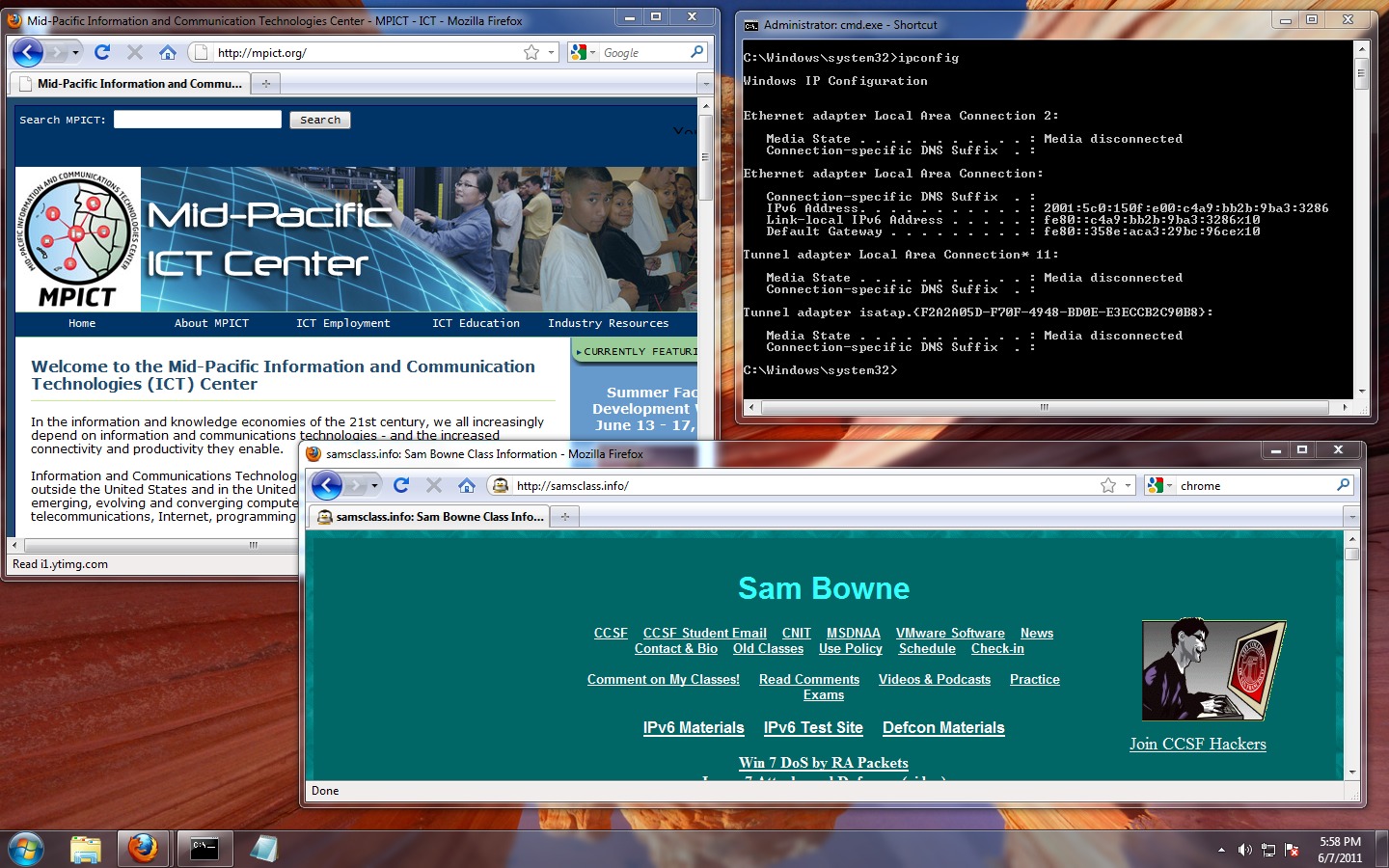
Last Modified: 3-21-16
